Researchers from North Carolina State University and the University of Oregon show how hackers can anonymously hijack computing power from cloud-based Web browsers.
Cloud-based browsing is intended to boost the performance of low-power devices, like mobile phones and tablets, by offloading the bulk of the computation to remote servers. However, by exploiting design vulnerabilities inherent in some cloud browsers, cyber-thieves can create a virtual compute farm dedicated to unlawful activities, like password cracking and denial of service attacks.
A new research paper, Cloud-Based Browsers for Fun and Profit, describes the parasitic computing ploy in detail. Considering the powerful capabilities of today’s cloud browsers, the researchers wondered: “Was it now possible to perform arbitrary general-purpose computation within cloud-based browsers, at no cost to the user?”
A technique called Browser MapReduce (BMR) is used to explore the computation and memory limits of four cloud browsers, Amazon Silk, Opera Mini, Cloud Browse and Puffin. BMR is based on Google’s MapReduce framework for the parallel processing of large datasets.
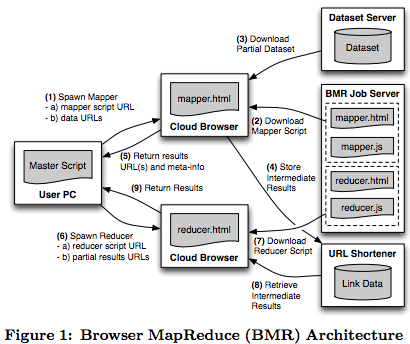
The researchers developed and tested three canonical MapReduce applications – word count, distributed grep, and distributed sort. A URL shortening service was used to pass large packets of data between nodes. The computations were completed successfully, but due to ethical considerations, packet sizes were kept to 100 MB or less. Researcher and co-author, Dr. William Enck, an assistant professor of computer science at NC State, suggests that the same applications could be carried out using much larger datasets, they just didn’t want this academic exercise to pose an undue burden to the systems they were using.
Based on their findings and observations, the authors conclude that “the computational ability made freely available by cloud browsers allows for an open compute center that is valuable and warrants substantially more careful protection.”
As one example of the potential for misuse, they simulated a password cracking implementation and found that with Puffin, 24,096 hashes could be generated per second for a total of 200 million per job.
The paper provides several recommendations aimed at improving the security of cloud-based browsers.
1. Providers should place resource limitations on rendering tasks.
2. Because a framework such as BMR can link jobs to create a computation grid, providers should also rate limit connections from mobile clients. One way to do this is to require users to create accounts, and place rate limits on authenticated users.
3. To help reduce the ability to clone instances, the browser could require registration and use a device-specific private key as part of its handshake protocol with the cloud-based renderers. The Amazon Silk browser already does this.
4. Techniques such as CAPTCHAs can limit the rate of creating new accounts.
The paper will be presented this Thursday at the Annual Computer Security Applications Conference in Orlando, Fla.




























































